ASA 8.2: Port Redirection (Forwarding) with nat, global, static, and access-list Commands Using ASDM - Cisco
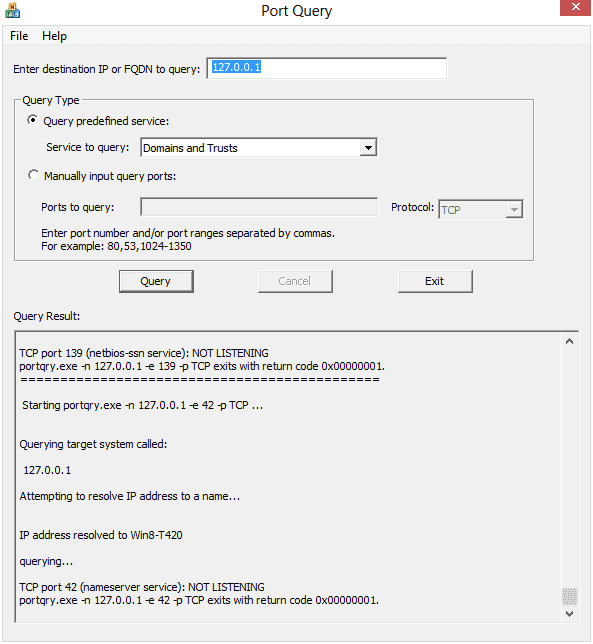
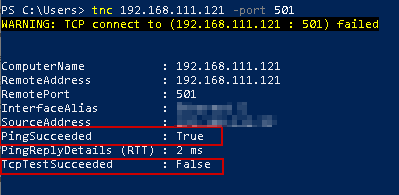
Troubleshooting TCP/IP Connectivity Issues with This Command-Line Utility Portqtry.exe - NEXTOFWINDOWS.COM
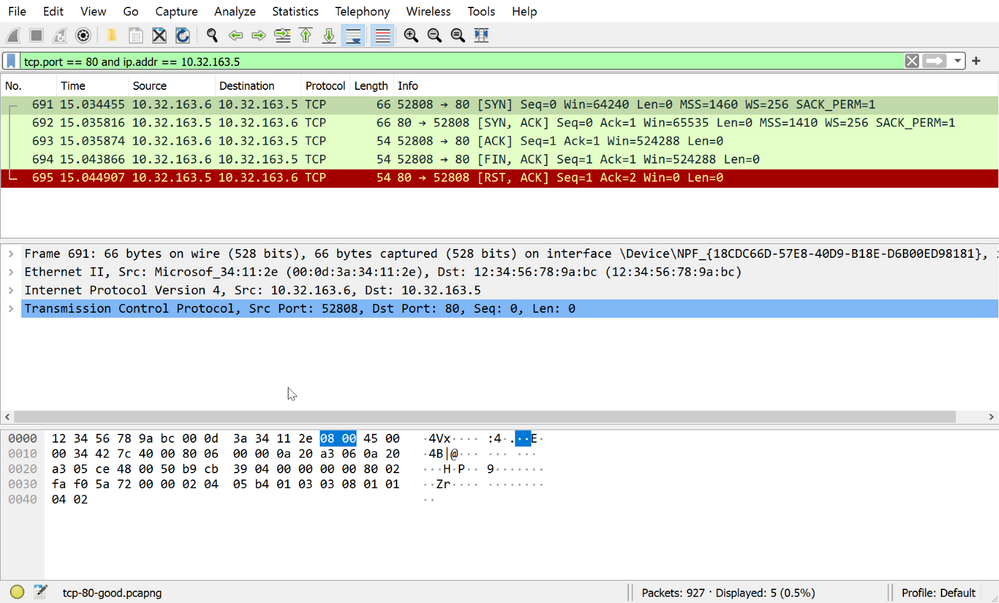
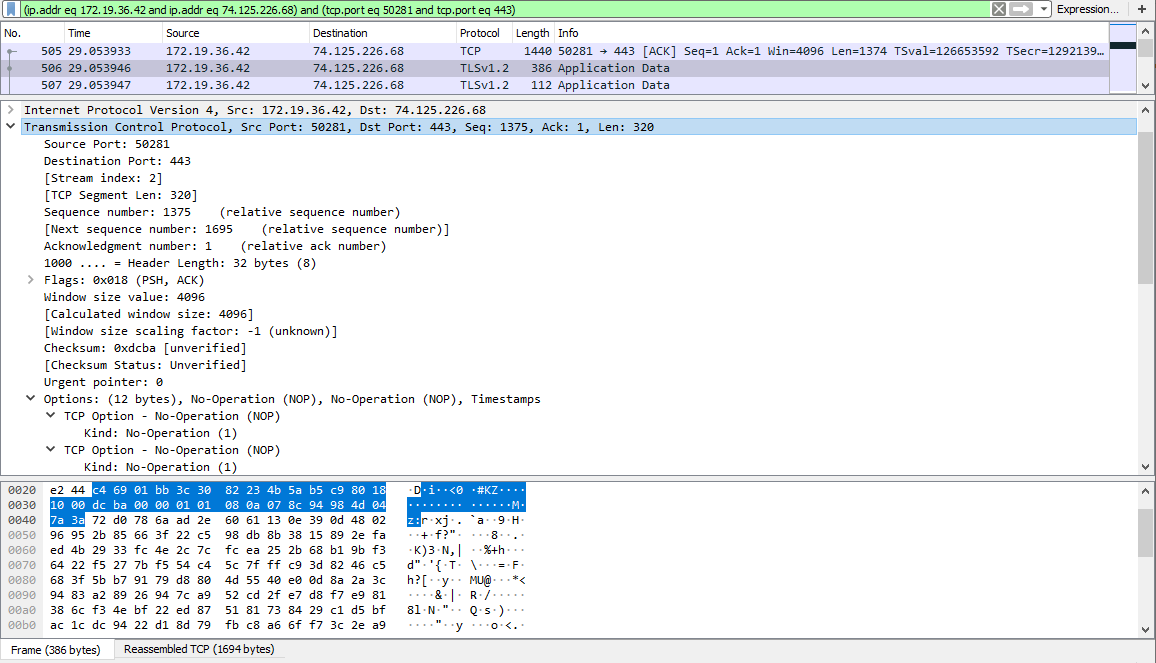
1. What is the IP address and TCP port number used by your client computer (source) to transfer the file to spinlab.wpi.edu? My

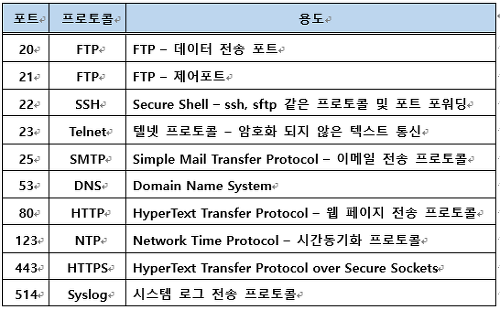
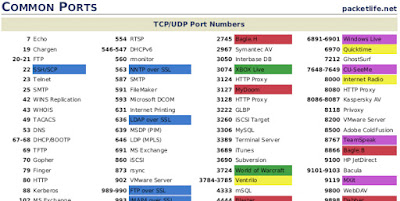
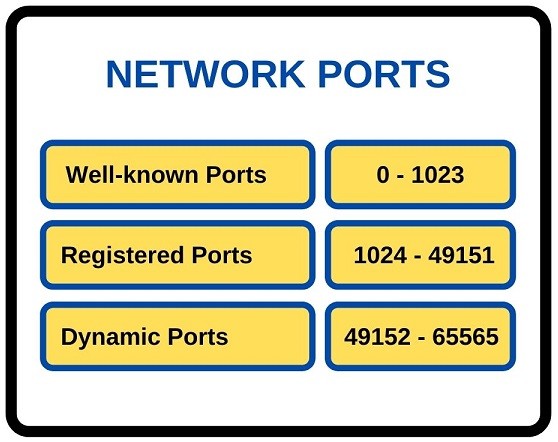
Interview #common #questions TCP/UDP port numbers. For cyber security professionals you can also think about the payloads you can use if these ports are open. #indincybersecuritysolutions #cybersecurity... - Indian Cyber Security Solutions -

TCP/IP and Ethernet Quick Reference Guide: From the OSI Model to port definitions, packet structure and subnetting: Yesmar, K: 9798419391956: Amazon.com: Books

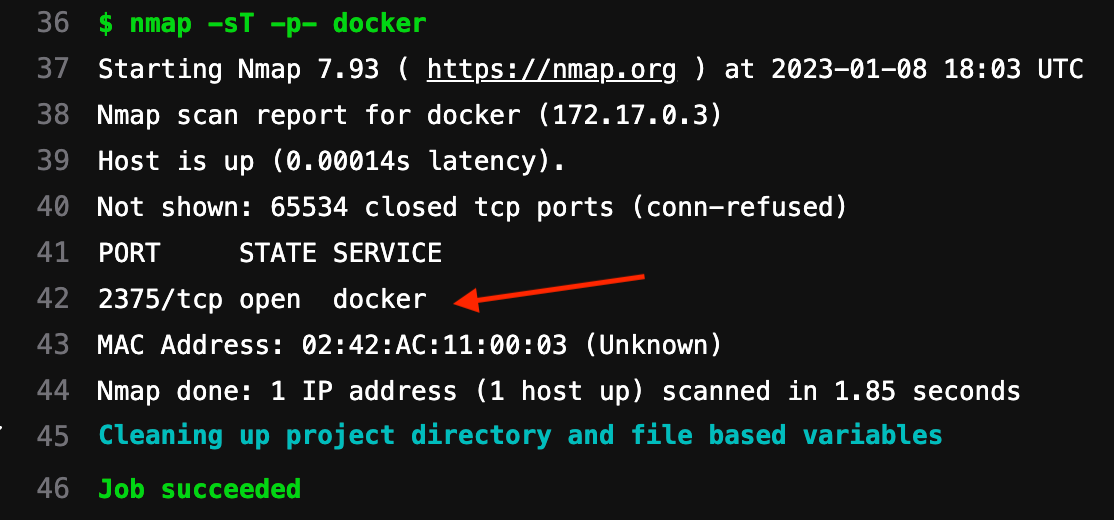
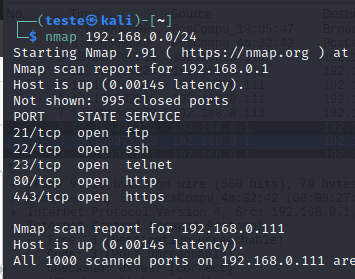
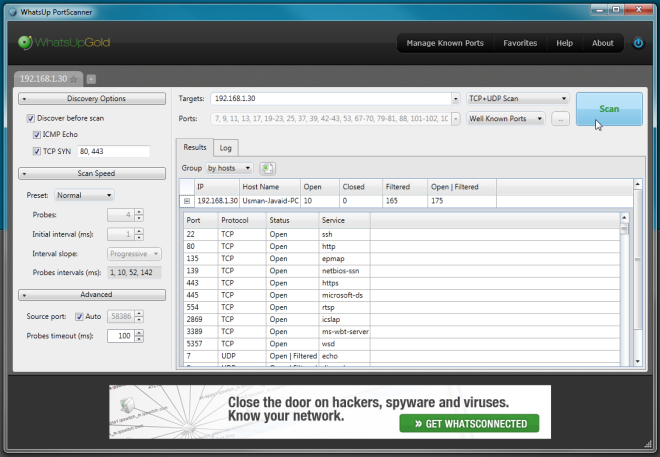
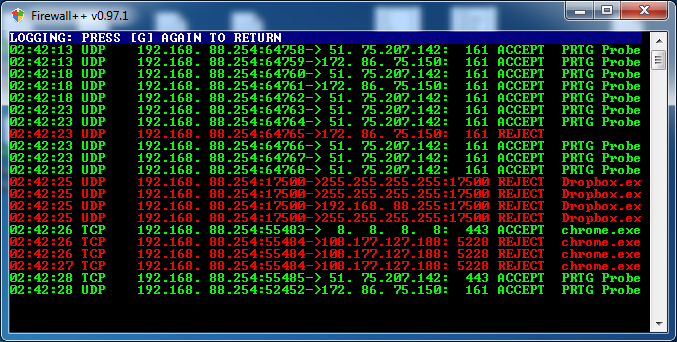
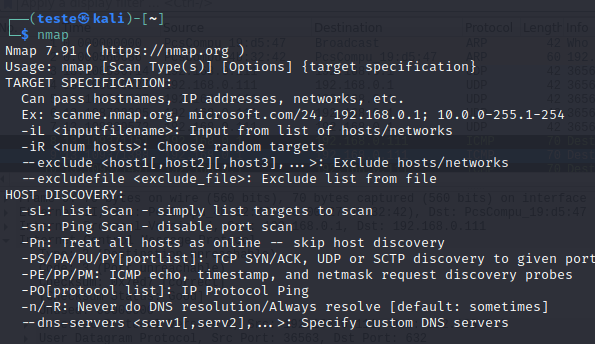
Day 46: How Do Hackers Use Open Ports To Perform Attacks? | Day 46: How Do Hackers Use Open Ports To Perform Attacks? Today I will discuss: 1. Why do hackers search